At Experts Live Denmark 2026, Raviv Tamir — Vice President and Chief Product Strategy for SIEM & XDR at Microsoft — delivered a keynote that should make every security leader pause and reconsider their assumptions.
Not a product pitch. Not a roadmap update. A candid, sometimes uncomfortable reflection on what defenders are learning the hard way as attacks become faster, more coordinated, and increasingly AI-driven.
The central message was simple and unsettling: if attackers have a better map of your organization than you do, you’re already losing.
The Old Playbook Is Dead
Picture a typical Tuesday in a security operations center. An alert fires. An analyst investigates, confirms attacker presence, and begins containment. Historically, this was the turning point — once discovered, attackers would retreat, hide, or abandon the operation altogether.
That assumption is now dangerously outdated.
In recent major incidents — including attacks against Microsoft’s own environment — something new happened. The attackers knew they had been detected. They understood what the defenders knew. And they continued the attack anyway.
Think about what that means for a moment. Detection alone is no longer a deterrent. The attacker on the other end of that keyboard isn’t panicking when your SIEM fires an alert. They’re adapting. They’re accelerating. And with AI in their toolkit, they’re compressing what used to take days into hours — or less.
In some cases, attackers appeared to have a more complete understanding of Microsoft’s own environment than the internal defenders did.
The Story of a Million Shadow Tenants
Here’s a story that should keep every Azure administrator up at night.
During an investigation, Microsoft discovered that an attacker had found an over-privileged application sitting in a satellite tenant — created years earlier for demos or testing, long forgotten by the teams that built it. The attacker identified it, compromised it, and leveraged its permissions to pivot straight into the core environment.
When Microsoft asked the obvious follow-up question — how many similar tenants exist? — the answer was staggering: over one million shadow tenants, many without full security coverage.
One million forgotten doors. One million potential entry points. One million reasons why the old “secure the perimeter” thinking has become a fairy tale.
Two painful truths emerged:
- The edges of your environment are where you’re most exposed. Not your flagship production tenant — the demo environment someone spun up three years ago and never decommissioned.
- You can’t defend what you can’t see. And most organizations have far more blind spots than they realize.
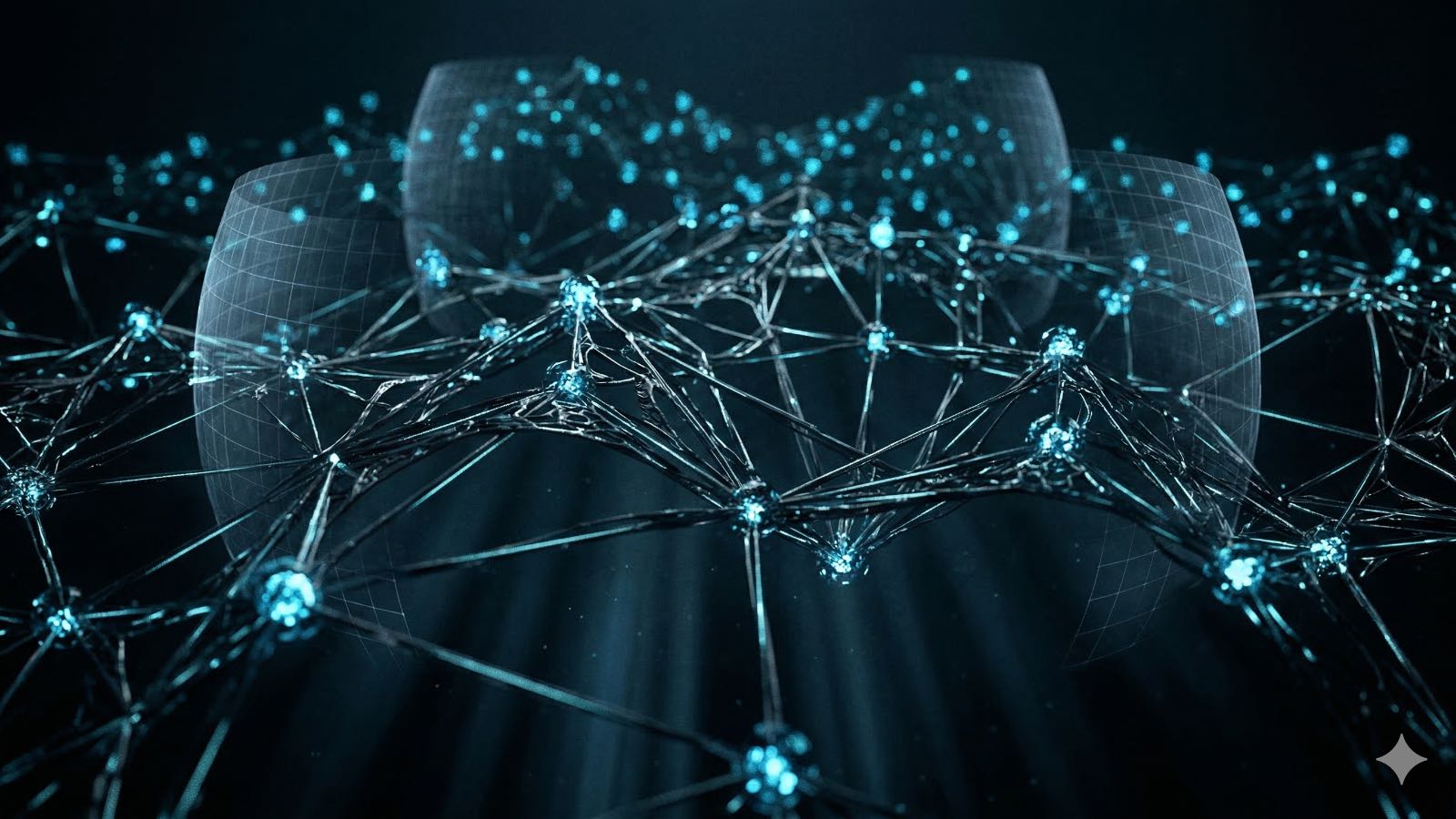
Attackers Think in Graphs. Defenders Think in Lists.
This insight, originally articulated by John Lambert, sits at the heart of Microsoft’s evolving defense strategy — and it’s one I keep coming back to in my own work with organizations.
Attackers don’t care about your domain boundaries, your tooling decisions, or your org chart. They care about paths — how to traverse from one asset to another until they reach their target. They see your environment as a connected graph of relationships, permissions, and trust chains.
Defenders, meanwhile, have traditionally worked with lists. Lists of vulnerabilities. Lists of alerts. Lists of patches. Lists of users.
That mismatch creates a dangerous asymmetry. The attacker sees a web of interconnected paths. The defender sees a spreadsheet.
The answer is a graph-based model of your organization:
- Assets become nodes
- Relationships become edges
- Attack paths become visible
Not as an abstract concept pinned to a whiteboard — but as an operational foundation that changes how you prioritize, how you respond, and how you anticipate.
Stop Boiling the Ocean
Here’s where the graph model transforms from interesting theory into practical strategy.
Trying to secure everything equally is impossible. Every organization knows this, yet most still spread their resources thin across an ever-expanding attack surface. The graph enables a fundamental shift in thinking.
Instead of asking “How do we fix every vulnerability?” the question becomes: “What are our critical assets, and how can attackers reach them?”
The numbers are compelling: critical assets often represent roughly 1% of total assets. The attack paths leading to them are a much smaller, manageable subset of all possible vulnerabilities. And here’s the key insight — to break an attack path, you don’t need to fix everything. You only need to remove or control one edge.
One misconfigured permission. One excessive privilege. One unnecessary trust relationship. Remove it, and an entire attack path collapses.
That reframing turns an overwhelming, never-ending problem into a solvable one.
When Minutes Decides Everything
Let me paint another picture. An active attack is underway. The attacker has gained initial access, is moving laterally, and is escalating privileges. Your SOC team is scrambling.
In one real-world example shared during the keynote, Microsoft’s automated systems executed hundreds of defensive actions within 50 minutes during an active attack. Isolating compromised accounts. Revoking tokens. Blocking lateral movement. Containing blast radius.
No human SOC — no matter how talented, no matter how caffeinated — can operate at that pace.
This has led to what Raviv described as a “fire first, ask questions later” model:
- High-confidence threats trigger immediate automated response
- Humans investigate once the attack is paused
- The system continues reacting as the attacker pivots
This approach is now enabled by default for certain threat classes, including ransomware and hands-on-keyboard attacks. The philosophy is clear: an imperfect automated response executed in seconds beats a perfect human response delivered minutes too late.
Predictive Shielding: Playing Chess, Not Checkers
With a graph model in place, defenders can move beyond reaction into prediction.
Instead of blindly isolating everything when an attack is detected, the system can ask contextual questions: What is this asset? What role does it play? How aggressive can we be without breaking the business?
Defensive actions become surgical:
- Temporarily tightening policies on exposed assets
- Blocking specific lateral movement connections
- Selectively isolating downstream resources that sit in the likely attack path
The goal isn’t disruption for its own sake — it’s precision containment. Think of it as the difference between flooding an entire building to put out a fire and deploying a targeted suppression system that protects the critical rooms while containing the damage.
The AI Paradox in the SOC
AI is reshaping the SOC, but not in the way most vendor marketing suggests. Raviv described three emerging patterns:
- Augmenting humans — AI as copilot, accelerating investigation and triage
- Delegating tasks — autonomous agents handling routine response
- Agents as team members — AI embedded into workflows as persistent participants
But there’s an often-overlooked problem: AI accelerates senior analysts dramatically — but can mislead juniors if left unchecked. Without structured learning paths, organizations risk hollowing out the pipeline that creates future security experts. The senior analysts get faster; the junior analysts never learn to think critically because the AI does it for them.
One innovative approach shared was transcribing analyst actions inside the SOC — capturing investigation steps, generating case notes automatically, identifying repetitive tasks for automation, and comparing real behavior against standard operating procedures. This turns AI into both a productivity engine and a training tool.
The New Blueprint
The keynote closed with a framework that I believe every security leader should internalize:
- Graphs provide the map
- AI provides the speed
- Automation provides the scale
- Humans provide the judgment
None of these alone is sufficient. A graph without automation is just a pretty picture. Automation without a graph is just fast chaos. AI without human judgment is a liability. And humans without any of these tools are simply outgunned.
A Question You Should Be Asking Tomorrow Morning
Here’s what I want you to take away from this.
Right now, somewhere in your environment, there’s a forgotten service principal with excessive permissions. A shadow tenant that nobody monitors. A trust relationship that creates a direct path from your least-secured asset to your crown jewels. An attack path that an adversary could traverse in hours while your team debates the priority of a vulnerability ticket.
Do you know what your critical assets are? Do you know the paths that lead to them? And do you know which single edge, if removed, would collapse the most dangerous of those paths?
If you can’t answer those questions, the attackers already have a better map than you do.
The future of security isn’t about buying more tools or hiring more analysts. It’s about seeing your environment the way your adversaries do — as a connected graph of opportunities — and moving faster than they can adapt.
Start with the graph. Everything else follows.